
Download the free Kindle app and start reading Kindle books instantly on your smartphone, tablet, or computer - no Kindle device required.
Read instantly on your browser with Kindle for Web.
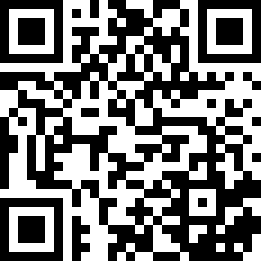
Using your mobile phone camera - scan the code below and download the Kindle app.
An Introduction to Mathematical Cryptography (Undergraduate Texts in Mathematics) Softcover reprint of hardcover 1st ed. 2008 Edition
Purchase options and add-ons
- ISBN-101441926747
- ISBN-13978-1441926746
- EditionSoftcover reprint of hardcover 1st ed. 2008
- Publication dateDecember 1, 2010
- LanguageEnglish
- Dimensions6.1 x 1.22 x 9.25 inches
- Print length540 pages
There is a newer edition of this item:
Frequently bought together

Customers who viewed this item also viewed
Editorial Reviews
Review
From the reviews:
"The book is devoted to public key cryptography, whose principal goal is to allow two or more people to exchange confidential information … . The material is very well organized, and it is self-contained: no prerequisites in higher mathematics are needed. In fact, everything is explained and carefully covered … . there is abundance of examples and proposed exercises at the end of each chapter. … This book is ideal as a textbook for a course aimed at undergraduate mathematics or computer science students." (Fabio Mainardi, The Mathematical Association of America, October, 2008)
"This book focuses on public key cryptography … . Hoffstein, Pipher, and Silverman … provide a thorough treatment of the topics while keeping the material accessible. … The book uses examples throughout the text to illustrate the theorems, and provides a large number of exercises … . The volume includes a nice bibliography. … Summing Up: Highly recommended. Upper-division undergraduate through professional collections." (C. Bauer, Choice, Vol. 46 (7), March, 2009)
"For most undergraduate students in mathematics or computer science (CS), mathematical cryptography is a challenging subject. … it is written in a way that makes you want to keep reading. … The authors officially targeted the book for advanced undergraduate or beginning graduate students. I believe that this audience is appropriate. … it could even be used with students who are just learning how to execute rigorous mathematical proofs. … I strongly believe that it finds the right tone for today’s students … ." (Burkhard Englert, ACM Computing Reviews, March, 2009)
"The exercises and text would make an excellent course for undergraduate independent study. … This is an excellent book. Hoffstein, Pipher and Silverman have written as good a book as is possible to explain public key cryptography. … This book would probably be best suited for a graduate course that focused on public key cryptography, for undergraduate independent study, or for the mathematician who wants to see how mathematics is used in public key cryptography." (Jintai Ding and Chris Christensen, Mathematical Reviews, Issue 2009 m)
From the Back Cover
This self-contained introduction to modern cryptography emphasizes the mathematics behind the theory of public key cryptosystems and digital signature schemes. The book focuses on these key topics while developing the mathematical tools needed for the construction and security analysis of diverse cryptosystems. Only basic linear algebra is required of the reader; techniques from algebra, number theory, and probability are introduced and developed as required.
The book covers a variety of topics that are considered central to mathematical cryptography. Key topics include:
* classical cryptographic constructions, such as Diffie-Hellmann key exchange, discrete logarithm-based cryptosystems, the RSA cryptosystem, and digital signatures;
* fundamental mathematical tools for cryptography, including primality testing, factorization algorithms, probability theory, information theory, and collision algorithms;
* an in-depth treatment of important recent cryptographic innovations, such as elliptic curves, elliptic curve and pairing-based cryptography, lattices, lattice-based cryptography, and the NTRU cryptosystem.
This book is an ideal introduction for mathematics and computer science students to the mathematical foundations of modern cryptography. The book includes an extensive bibliography and index; supplementary materials are available online.
About the Author
Dr. Jeffrey Hoffstein has been a professor at Brown University since 1989 and has been a visiting professor and tenured professor at several other universities since 1978. His research areas are number theory, automorphic forms, and cryptography. He has authored more than 50 publications.
Dr. Jill Pipher has been a professor at Brown Univesity since 1989. She has been an invited lecturer and has received numerous awards and honors. Her research areas are harmonic analysis, elliptic PDE, and cryptography. She has authored over 40 publications.
Dr. Joseph Silverman has been a professor at Brown University 1988. He served as the Chair of the Brown Mathematics department from 2001–2004. He has received numerous fellowships, grants and awards and is a frequently invited lecturer. His research areas are number theory, arithmetic geometry, elliptic curves, dynamical systems and cryptography. Hehas authored more than120 publications and has had more than 20 doctoral students.
Product details
- Publisher : Springer
- Publication date : December 1, 2010
- Edition : Softcover reprint of hardcover 1st ed. 2008
- Language : English
- Print length : 540 pages
- ISBN-10 : 1441926747
- ISBN-13 : 978-1441926746
- Item Weight : 1.6 pounds
- Dimensions : 6.1 x 1.22 x 9.25 inches
- Best Sellers Rank: #1,135,229 in Books (See Top 100 in Books)
- #213 in Number Theory (Books)
- #288 in Computer Cryptography
- #301 in Web Encryption
- Customer Reviews:
About the authors

Discover more of the author’s books, see similar authors, read book recommendations and more.

Discover more of the author’s books, see similar authors, read book recommendations and more.

Discover more of the author’s books, see similar authors, read book recommendations and more.
Customer reviews
Customer Reviews, including Product Star Ratings help customers to learn more about the product and decide whether it is the right product for them.
To calculate the overall star rating and percentage breakdown by star, we don’t use a simple average. Instead, our system considers things like how recent a review is and if the reviewer bought the item on Amazon. It also analyzed reviews to verify trustworthiness.
Learn more how customers reviews work on AmazonCustomers say
Customers find the book readable and well-written, with one review noting it provides clear explanations and concrete examples. They appreciate the information quality, with one customer highlighting how it guides readers through different mathematical areas.
AI Generated from the text of customer reviews
Select to learn more
Customers find the book's information quality positive, with one customer noting how it guides readers through different areas of mathematics, while another mentions that each concept is presented cleanly.
"...studied by this reviewer, the authors of this book give an effective introduction to the mathematical theory used in cryptography at a level that..." Read more
"...It's an undergraduate textbook, guiding you through the different areas of math that are related to modern cryptography and to each other, with..." Read more
"...is both readable and provides sufficient background to provide context to the reader. Highly recommended." Read more
"Good start to this topic. The only hiccup was that I tried to work through the text example myself and came up with different answers...." Read more
Customers find the book very readable with good writing, and one customer mentions it includes easy-to-understand concrete examples.
"The good: The writing is VERY good, with each concept presented cleanly and in a cheerful tone. Reading this book wasn't just informative...." Read more
"...This book is a refreshing departure. The book is both readable and provides sufficient background to provide context to the reader...." Read more
"...It is so clear, and many time teaches by using easy to understand concrete examples...." Read more
"...background for an array of subjects and has allowed me to pick up the subject quite easily." Read more
Top reviews from the United States
There was a problem filtering reviews. Please reload the page.
- Reviewed in the United States on December 17, 2009At least for the chapters that were studied by this reviewer, the authors of this book give an effective introduction to the mathematical theory used in cryptography at a level that can be approached by an undergraduate senior in mathematics. The field of cryptography is vast of course, and a book of this size could not capture it effectively. The topics of primary importance are represented however, and the authors do a fine job of motivating and explaining the needed concepts.
The authors give an elementary overview of elliptic curves over the complex numbers, and most importantly over finite fields whose characteristic is greater than 3. The case where the characteristic is equal to 2 is delegated to its own section. In discussing the arithmetic of elliptic curves over finite fields, the authors give a good motivation for Hasse's formula, which gives a bound for the number of points of the elliptic curve (over a finite field), but they do not go into the details of the proof. The Hasse formula is viewed in some texts as a "Riemann Hypothesis" for elliptic curves over finite fields, and was proven by Hasse in 1934. This reviewer has not studied Hasse's proof, but a contemporary proof relies on the Frobenius map and its separability, two notions that the authors do not apparently want to introduce at this level of book (however they do introduce the Frobenius map when discussing elliptic curves over F2). Separability is viewed in some texts in elliptic curves as more of a technical issue, which can be ignored at an elementary level. It arises when studying endomorphisms of elliptic curves of fields of non-zero characteristic, and involves defining rational functions. The Frobenius map is not separable, and this fact allows one to show that its degree is strictly greater than the number of points in its kernel. Taking the nth power of the Frobenius map and adding to it the endomorphism which simply multiplies elements by -1, one can show that the number of points of the elliptic curve is equal to the degree of this endomorphism. Just a few more arithmetical calculations establishes Hasse's estimate.
Some more of the highlights of this part of the book:
- The reminder that the fastest known algorithm to solve the elliptic curve discrete logarithm problem takes p^1/2 steps for a finite field Fp (i.e. the algorithms therefore are not really better than "black box" algorithms).
- The brief historical discussion on public key cryptography.
- The motivational discussion for the Lenstra algorithm using simple calculations that leads to a failed attempt to find the reciprocal of an integer modulo p. This failure is used to explain the workings of the Lenstra elliptic curve factorization algorithm in a way that it is better appreciated by the reader.
- The discussion on the Frobenius map in the context of elliptic curves over F2 and its use in finding the number of points of an elliptic curve over a finite field.
- The motivational discussion for the use of distortion maps, due to the degeneracy of the Weil pairing. The distortion maps are used to define a modified Weyl pairing, which is proved to be non-degenerate.
Some omissions:
- Algorithms used to calculate the number of points of an elliptic curve over a finite field that are more efficient than brute-force counting or estimation using Hasse's formula.
- The proof that the torsion points of order m can be written as the product of two cyclic groups of order m. The authors apparently do not want to get into the notions of unramified and separable "isogenies" between elliptic curves and Galois extensions, both of which are used in the proof that they reference. Isogenies are mentioned in a footnote to the discussion on distortion maps, since the latter are isogenies.
- The proof verifying certain properties of divisors, namely that they are equal if the corresponding rational functions are constant multiples of each other, and that the degree of a divisor is zero if its sum is the zero element of the elliptic curve. The proofs were no doubt omitted due to their dependence on techniques from algebraic geometry.
- Quantum cryptography. This is discussed very briefly in the last chapter, but the subject is mature enough to be presented at the undergraduate level.
- Cryptography based on non-Abelian groups. One good example would be cryptography based on the mathematical theory of knots and braids (the braid group is non-Abelian), even though this approach is in its infancy at the present time, and in almost all cases shown to be highly vulnerable to attacks. It could have been included in the last chapter or possibly as a long exercise.
- Hyperelliptic curves are discussed very briefly in the last chapter, but a full-fledged presentation could be done in the book without missing the targeted audience. Hyperelliptic curves are also mentioned after the discussion of the MOV algorithm, wherein the authors allude to the use of Weil descent to transfer the elliptic curve discrete logarithm problem to a discrete logarithm problem in a finite field F2^m when m is composite. The authors correctly don't want to elaborate on Weil descent in any more detail, since it requires a solid knowledge of field extensions and theory of algebraic varieties at a level that one obtains in a graduate course in algebraic geometry. Suffice it to say that the strategy of Weil descent involves finding a cover of the elliptic curve by a hyperelliptic curve that is defined over the extension of the ground field. This approach has been shown to be problematic for Koblitz curves, the latter of which are discussed in the book.
Note: This review is based on a reading of chapters 5 and 8 of the book.
- Reviewed in the United States on June 10, 2021Format: PaperbackVerified PurchaseThe good: The writing is VERY good, with each concept presented cleanly and in a cheerful tone. Reading this book wasn't just informative. It was fun! I definitely plan to use it for my cryptography class next fall.
The topics also proceed in a sensible order, both for self-study and for a class. It isn't an encyclopedia, covering all facts about modern cryptography. It's an undergraduate textbook, guiding you through the different areas of math that are related to modern cryptography and to each other, with enough real-world examples to keep your interest.
All of the algorithms are explained carefully and then you're expected to actually use them in examples that are too big to do by hand (but are still small enough to easily crack with a computer). After a while, the fact that certain operations are easy and others are hard really sinks in.
The bad: The level of sophistication expected of readers jumps up and down wildly, especially towards the back of the book. In the span of a few pages you might go from some subtle facts about algebraic geometry, stated without proof, back down to the definition of a vector space. If reading on your own, you probably will have to skip some of the harder stuff and will want to skim over the easy stuff. In a classroom, it's the instructor's job to provide that navigation.
The good greatly outweighs the bad. 5 stars.
- Reviewed in the United States on May 18, 2010I picked up this book to review before I recommend it to my team of system engineers. Most of the textbooks I review are a mess and seem to exist solely to egrandize the author and subidize a professor's lifestyle.
This book is a refreshing departure. The book is both readable and provides sufficient background to provide context to the reader.
Highly recommended.
- Reviewed in the United States on August 23, 2015Format: PaperbackVerified PurchaseGood start to this topic. The only hiccup was that I tried to work through the text example myself and came up with different answers. This is because the text was wrong. There is an extensive errata file that you can get online. May sure you get it before starting to work through text examples and end-of-chapter exercises. I hope that a revised version is issued that corrects these errata.
- Reviewed in the United States on April 13, 2023Format: PaperbackVerified PurchaseThe book also has good exercises at the end of chapters.
- Reviewed in the United States on March 15, 2014I'm doing my honor's thesis on theoretical Cryptography as an undergrad at Colby College, and this book has been the perfect resource. It is so clear, and many time teaches by using easy to understand concrete examples. This book is the perfect place to start if you want to learn about Crypto.
- Reviewed in the United States on October 22, 2012It is a great book that gives the intro and mathematical background for an array of subjects and has allowed me to pick up the subject quite easily.
- Reviewed in the United States on January 23, 2012Very good book. Not too complex even for someone like me with limited math skills who doesn't mind googling to go deeper into some of the more complex math.
Top reviews from other countries
 DrChaseReviewed in India on July 27, 2017
DrChaseReviewed in India on July 27, 20175.0 out of 5 stars Five Stars
Format: PaperbackVerified PurchaseGood book for ug study or may be in first yest of pg
 José Luis Castro GarcíaReviewed in Mexico on August 7, 2020
José Luis Castro GarcíaReviewed in Mexico on August 7, 20202.0 out of 5 stars Good book
Format: PaperbackVerified PurchaseThe content of the book is very good, but the binding arrived damaged.
-
 Fabrizio GuzzoReviewed in Italy on March 18, 2023
Fabrizio GuzzoReviewed in Italy on March 18, 20235.0 out of 5 stars Ottimo
Format: PaperbackVerified Purchasearrivato in buono stato. ottimo libro














